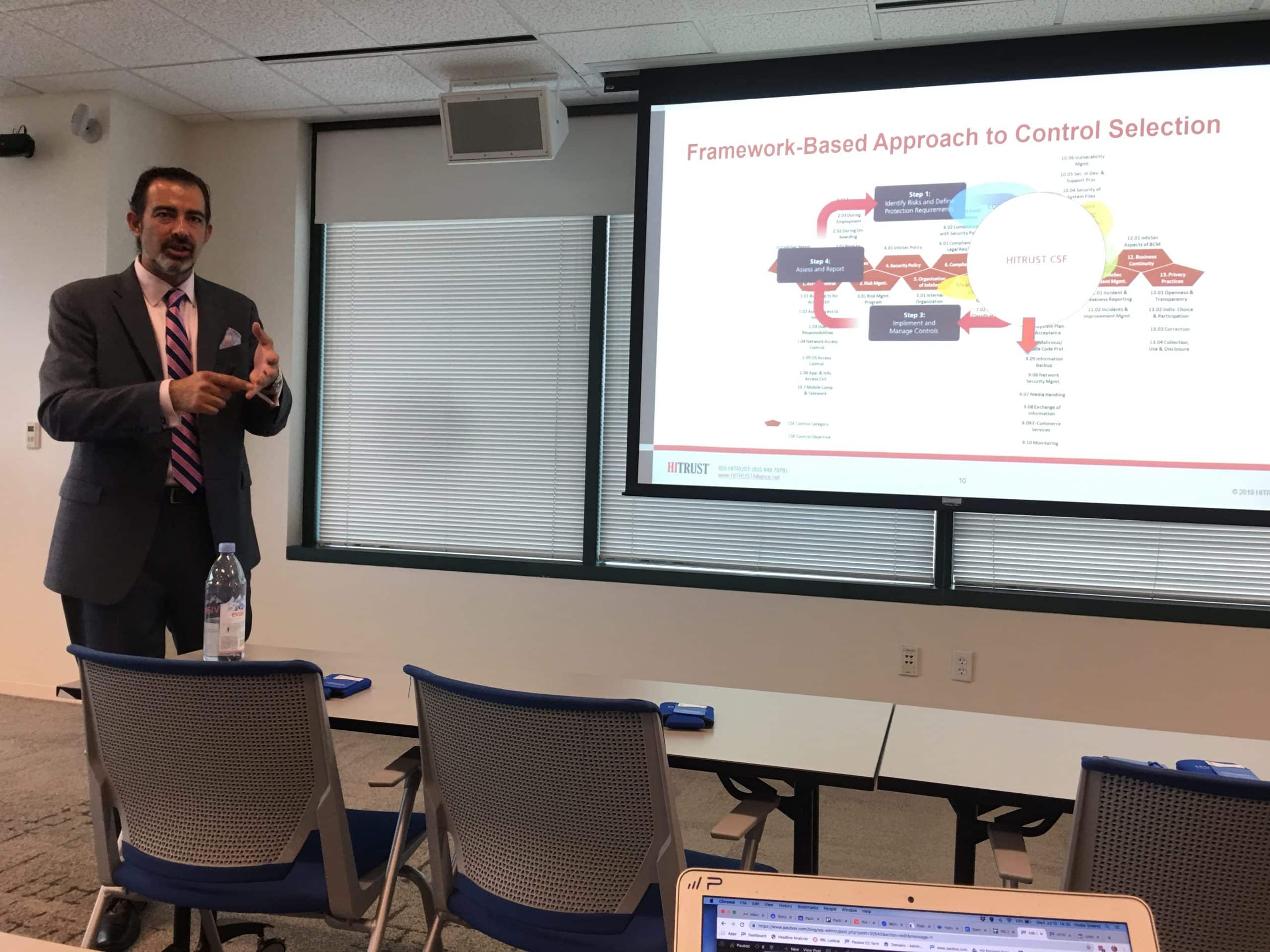
Last week we flew to Tampa to attend our first HITRUST Community Extension Program (CEP) event. It was sponsored by 360 Advanced and hosted at Microsoft’s office. Towards the end of the program, I discussed an idea about creating content around specific HITRUST controls that Paubox directly addresses. In other words, the goal would be to make it easier to find solutions that can help organizations achieve HITRUST CSF compliance. The idea was greeted with approval. This post is aimed to help organizations going through HITRUST certification find solutions that can help them achieve CSF Compliance for specific controls.
HITRUST Transmission Protection: Control 9.11
As of version 9.2 of the HITRUST CSF, here is the language for Control 9.11 (Transmission Protection): "The organization does not send PII/PHI over facsimile (FAX), unless it cannot be sent over other, more secure channels (e.g., delivery by hand, secure email)." I can distinctly recall this control, as we blogged about it during our HITRUST CSF Gap Analysis.
Illustrative Procedure for Policy
Within each HITRUST control, there's a section called "Illustrative Procedure for Policy." Its purpose is to help organizations understand the spirit of the control. We referred to them quite often when we were going through our HITRUST journey. Here's the Illustrative Procedure for Policy for Control 9.11 (Transmission Protection):"Examine policies and/or standards related to the use of fax communications and determine if the organization does not send PII/PHI over facsimile (FAX), unless it cannot be sent over other, more secure, channels (e.g., delivery by hand, secure email). If no written policy or standard exists, interview control owner(s) responsible for, key staff involved in/with, and/or other relevant stakeholders impacted by the policy/control requirement(s) and determine if the requirement(s) is/are understood. Evidence of ad hoc or informal policy may also be provided by observing individuals, systems and/or processes associated with responsibilities for the use of fax communications to determine if the policy requirements are generally understood and implemented consistently. Review any written procedure(s) or examine documentation associated with formal or ad hoc processes to determine if the requirement(s) is/are addressed consistently by the entity."
Given our stance towards faxing (we recently held a wake for the fax machine), we were encouraged by HITRUST's posture on the matter.
How we satisfied Control 9.11 (Transmission Protection)

To address and satisfy Control 9.11, we solved it by doing two things:
- We created a written policy around the use of fax machines (we don't allow their use)
- Instead of using a fax machine, we created another written policy that stated we are to use our own Encrypted Email solution instead.
Conclusion
By creating written policies around fax usage and coupling it with our own use of Paubox Email Suite, we were able to satisfy Control 9.11 (Transmission Protection) of the HITRUST CSF certification. We hope this post helps others on their HITRUST journey.
About HITRUST
Founded in 2007, HITRUST Alliance is a not-for-profit organization whose mission is to champion programs that safeguard sensitive information and manage information risk for organizations across all industries and throughout the third-party supply chain. In collaboration with privacy, information security and risk management leaders from both the public and private sectors, HITRUST develops, maintains and provides broad access to its widely adopted common risk and compliance management and de-identification frameworks; related assessment and assurance methodologies; and initiatives advancing cyber sharing, analysis, and resilience.
Subscribe to Paubox Weekly
Every Friday we'll bring you the most important news from Paubox. Our aim is to make you smarter, faster.



 Hoala Greevy
Hoala Greevy