The FBI’s cyber division has issued a flash alert on Hive ransomware, following a recent series of incidents. The group was notably linked to an attack on Memorial Health System in August, which led to significant delays in operations and patient care.
Designed to compromise business networks through double extortion, Hive ransomware has targeted at least 28 organizations since its first detection in June. Here’s what you need to know about key warning signs, how to respond, and the smartest ways to reduce your risk.
How does Hive ransomware work?
Hive ransomware utilizes a diverse combination of techniques to carry out attacks, making mitigation particularly difficult. Common approaches include sending phishing emails with malicious attachments to gain network access and leveraging Remote Desktop Protocol (RDP) for lateral movement.
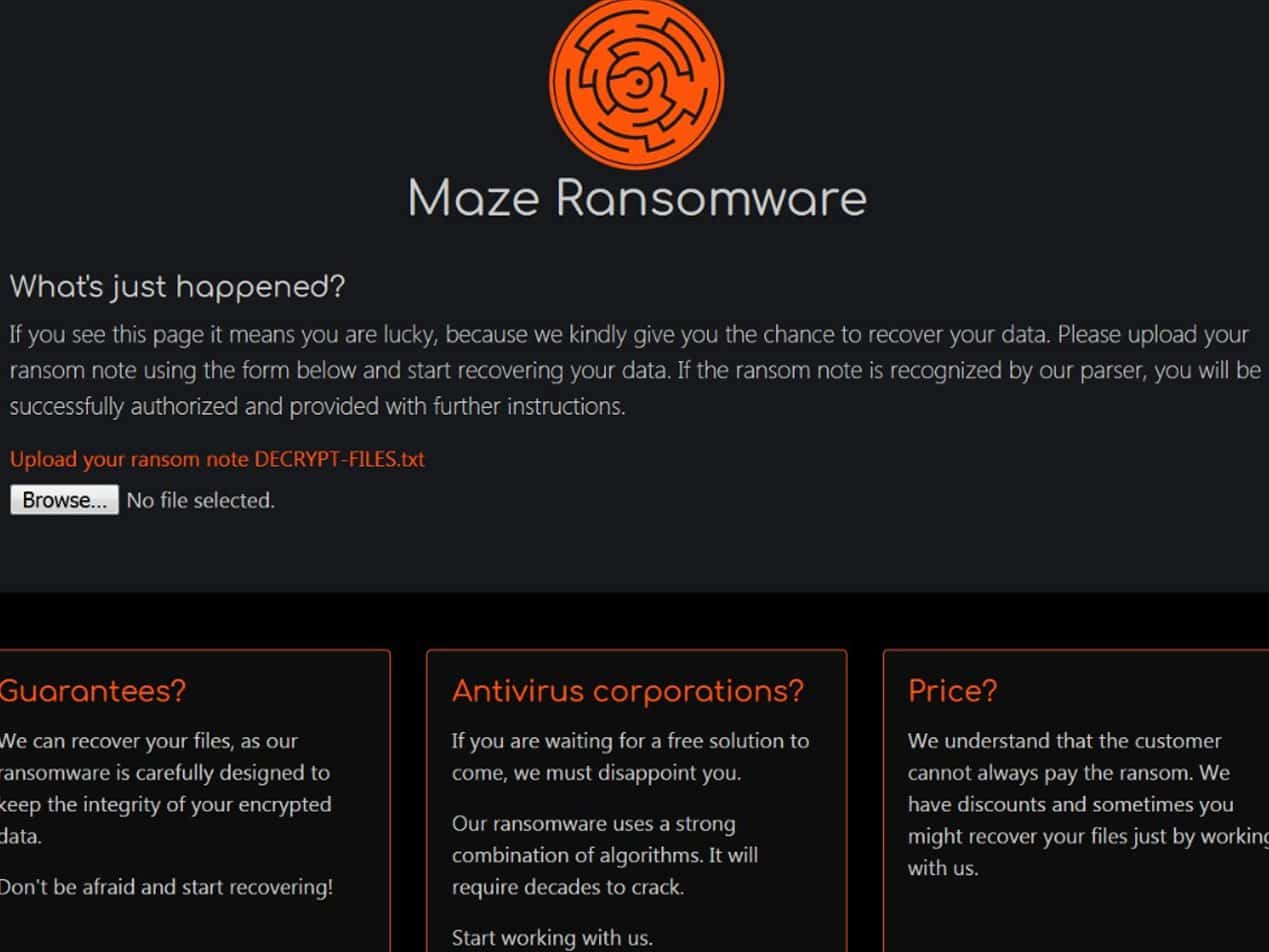
After successfully infiltrating a system, the threat actors move on to exfiltrating data and encrypting files. A ransom note is then left in each impacted directory, which outlines directions for purchasing the decryption software and threatens to leak the stolen information on the Tor site HiveLeaks. Payment deadlines typically span from two to six days and may be extended through further negotiation.
What are the recommendations?
The FBI strongly discourages paying a ransom, explaining that doing so may lead the actors to attack more organizations and incentivize other cybercriminals to engage in these activities. The alert also emphasizes that fulfilling the request does not always guarantee a full recovery of files.
Regardless of a company’s decision regarding payment, the FBI advises reporting all ransomware occurrences to your local field office. This enables investigators to hold attackers accountable, keep a closer eye on this emerging threat, and put a stop to future events.
Key indicators and prevention
The FBI’s alert includes a list of signs that a network may be infected, noting that many indicators can look like authentic programs with legitimate uses. As a precaution, the FBI suggests removing any applications that are not a vital component of your daily operations. Additional best practices include:
- Back up all critical information offline, storing copies in the cloud or on an external hard drive.
- Prioritize using two-factor authentication, including for remote services.
- Look out for cyber threat reports on compromised VPN credentials and change passwords or settings as needed.
- Make a habit of keeping all devices and applications up-to-date.
Take proactive action with Paubox
According to the American Health Association (AHA) , organizations in the healthcare sector may be especially vulnerable to this new strain of ransomware. With stronger email security measures in place, you can take extra steps to safeguard protected health information (PHI) and lower the chance of a costly attack.
Built to seamlessly integrate with your current email platform, Paubox Email Suite enables HIPAA compliant email by default and automatically encrypts every outgoing communication. This means that emails are sent straight to your patients’ inboxes, with no necessary passwords or portals to navigate.
Paubox’s Plus and Premium plan levels also come with innovative inbound email security tools that help get ahead of ransomware and other malicious threats. Our patented ExecProtect feature swiftly identifies and stops display name spoofing attempts, while Zero Trust Email requires one more unique piece of proof to confirm that a message is legitimate.
Subscribe to Paubox Weekly
Every Friday we'll bring you the most important news from Paubox. Our aim is to make you smarter, faster.